What is Intelligent IAM?
Intelligent IAM (IIAM) encompasses all the administrative processes used in Identity and Access Management (IAM), but the processes are influenced by real‐time data. IAM solutions that use intelligence continuously collect, monitor, and analyze large volumes of identity and access‐related information, combining data not only from provisioning and governance solutions but also from security products and other external systems. IIAM solutions are often designed to be used with a provisioning system, a governance system, or both.
- IIAM solutions, which include integrated identity analytics and intelligence (IAI), help find key information hidden in complexity and provide visibility into context and comparative data. These solutions may help organizations.
- Avoid security breaches by continuously monitoring for policy violations and vulnerabilities and by uncovering problems hidden in large volumes of data
- Strengthen risk management by reducing vulnerabilities immediately and by highlighting individuals and resources associated with high risks
- Continuously improve provisioning, governance, and other IAM processes by focusing attention on weak links and ineffective processes
- Improve the productivity of IT staffs by giving them tools to quickly and reliably conduct analyses, find patterns, identify anomalies, and spot trends
Why Is Traditional IAM No Longer Enough?
Until recently, traditional IAM encompassed only provisioning and governance products needed to evaluate or audit access to confirm that the access provided is in compliance with business policies and external governance regulations. Some examples of traditional IAM functionality include the following:
- Provisioning solutions automate the granting and revocation of access to applications, IT systems, and services; tangible assets such as laptops, smartphones, and security badges; and intangible entitlements such as access to secure areas.
- Governance solutions provide tools to enable compliance with government regulations, industry standards, and organization policies, and to verify that compliance.
- IAM solutions have helped organizations automate operations, reduce manpower needs, simplify audits, and provide users with access to the applications and resources they need. Yet traditional IAM processes are far from perfect.
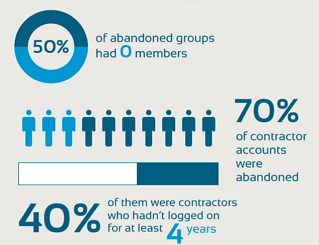
Organizations are still challenged by issues such as lingering abandoned accounts for users no longer affiliated with the organization, proliferating orphaned accounts with no administrative oversight, people with inappropriate access to data, and policy violations. These challenges increase the level of risk to the organization. In Figure 1-1 (right), you can see the impact abandoned accounts have on your organizations. With so many accounts left with no owner, you greatly increase your risk of a breach.
Get the Guide: 7 Identity and Access Management Fears
Identity and Access Management (IAM) doesn't have to be scary. IAM solutions can also show you what you can do to immediately secure your identities. Instead of giving you seven more reasons to run and hide, this book will give you seven reasons to overcome your fears of IAM.