Before I start, I need to come clean and tell you that I love enterprise software. Weird? Maybe. However, after working in the industry for many years and for many different companies, enterprise software is the basis for what drives business. Whether it’s your CRM, ERP or cyber security – it all starts with enterprise software.
I have worked in product management, marketing and operations over the years so I have a pretty good idea of what it takes to create and use software. It has to be user friendly, it has to be effective, and most of all, it has to do what the customer wants it to do.
I am happy to say that Core Security’s newest release, Access Assurance Suite 9.0 is the most beautiful identity experience. Ever.
Enterprise software is a lot of things and can do a lot of things - though, two words that you don’t typically associate with it are “beautiful” and “easy to navigate”.
But why not? If this platform can be made to do so many things, then why can’t we make it enjoyable to use? Why wouldn’t you want a nice interface if you’re going to be staring at this for hours every day? And wouldn’t you rather have something with easily recognized icons to save you time in looking for the right thing? Wouldn’t you rather accomplish a task in three clicks instead of seven?
What is the point of having the most powerful identity and access management software on the planet if it is too difficult to use?
While it’s a bold statement to make that we are delivering “The Most Beautiful Identity Experience”, the reality is that the market needs it right now. Identity and Access Management (IAM) software has been targeted towards IT users to enable business and process automation. While that’s nice, IAM has now gone mainstream. The users of IAM software now include everyone at the company. The users include employees requesting access to applications or managers in the business approving access - in addition to IT users who enable and provision that access. With that many users across the enterprise actively using IAM solutions, it requires a Consumer Grade Experience because the users of the software are consumers, too. This is why we have worked hard to deliver the most beautiful identity experience as this has become what the market needs today.
Ultimately, we create software intended to keep your company, and your employees, safe. Using this to its full extent can help you deter, detect, remediate and continuously validate your security posture against identity and access threats.
So, we dove into your most common problems and your most frequent tasks and set out on a mission to make those easier, more efficient and beautiful.
Let me show you two examples of how we have made this process more intuitive for our users:
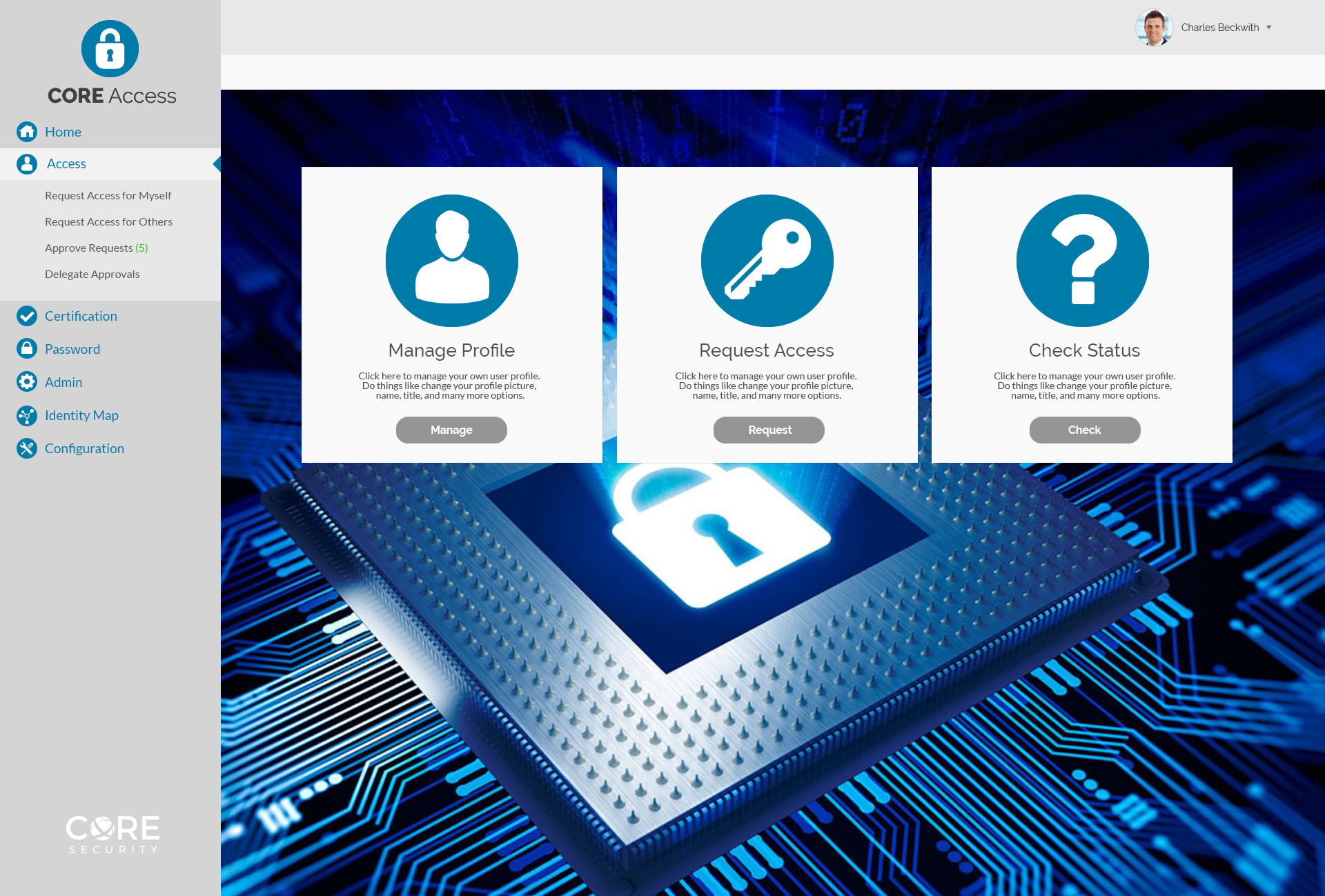
- Access Request Process – Here is our new access request dashboard. Want to request access? I dare you to miss it. With one click you are on your way to requesting access for any application you may need.
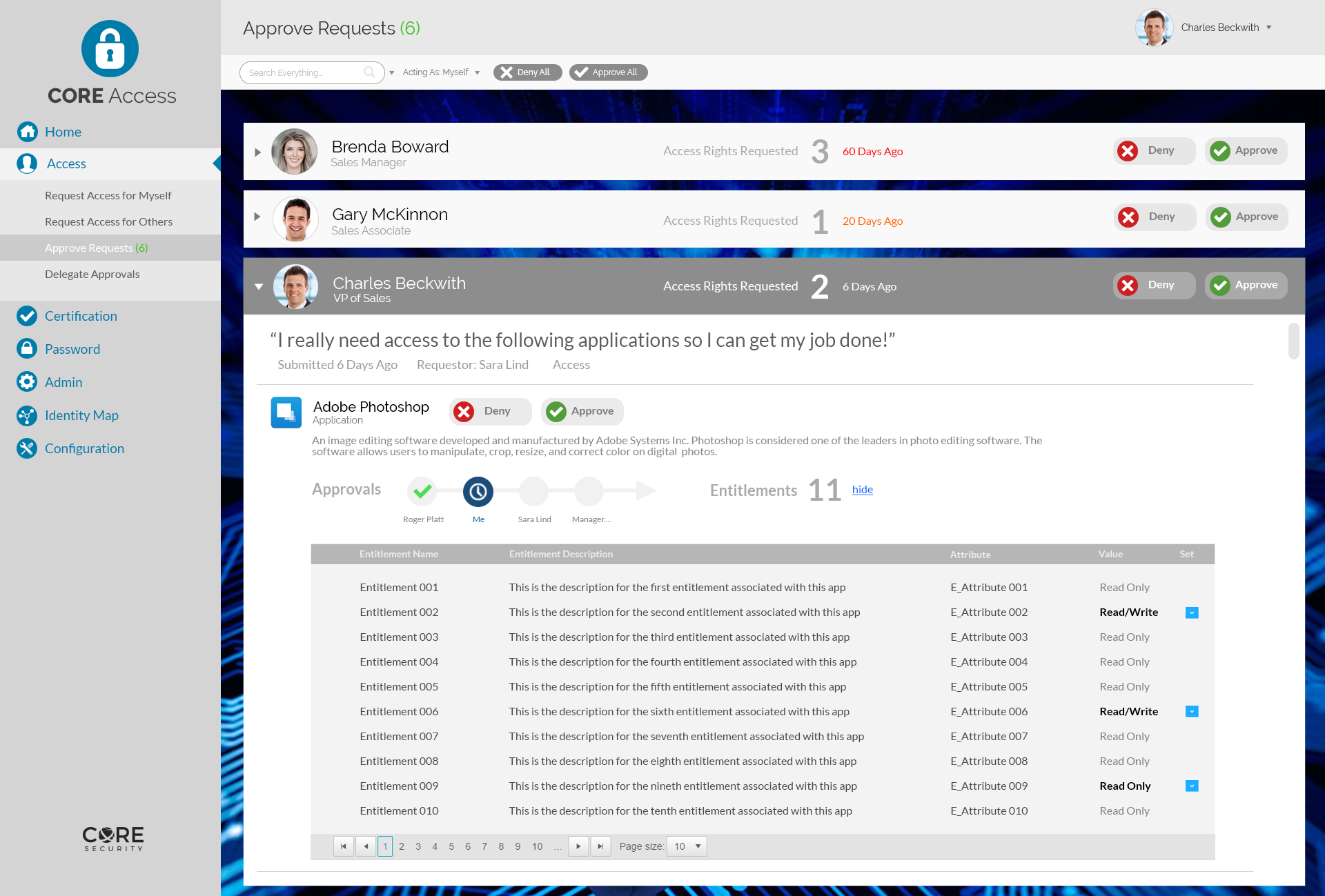
- Access Approvals Process – As a manager, you have a full schedule and guaranteeing access to all of your employees can be a tedious exercise. Take a look at our new approval request page. How many do you have to approve? Five. Without having to click around or try and find them, you know exactly what you have and with one click you are ready to go.